The VMProtect (www.vmpsoft.com) is a great commercial tool that can be used to protect Win32/64 native programs written by C++ or Delphi.
In one of my project, I use Delphi to create a COM DLL, and that is protected by the VMProtect 2.13. I use the following VMP settings.
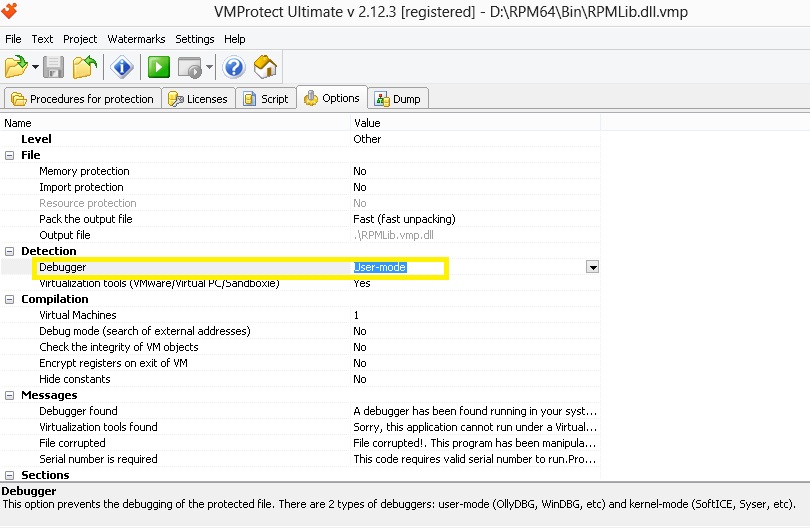
As you can see, I only enable the minimal checking of the ‘Debugger’. As described, there are two types of debuggers. One is user-mode (such as OlleyDBG, WinDBG) and the other kind is kernel mode, (such as SoftICE, syser etc). I guess the second one is more advanced and often used by hackers.
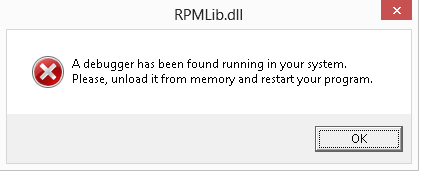
In the Messages sections, you can define the pop-up message to be shown when a debugger has been detected.
In Visual Studio (VS) 2010, you can easily create Windows application based on .NET platform. You can easily add COM reference to the project. For example,
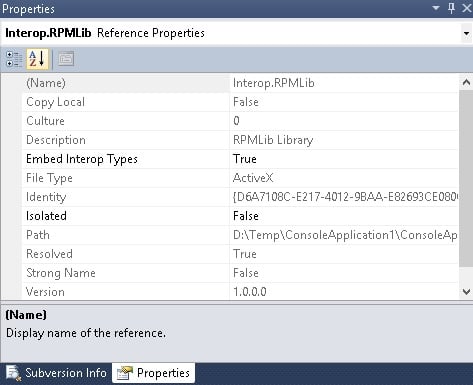
The VS will create a Type Library file (named Interop.*.dll) for each COM object. The ‘Embed’ option set to true will disable this. However, no matter what kind of configurations you have set in above property window, you will still have the debugger detected in .NET 4.0. But, the debugger detection is silent if you have .NET 3.5 or below.
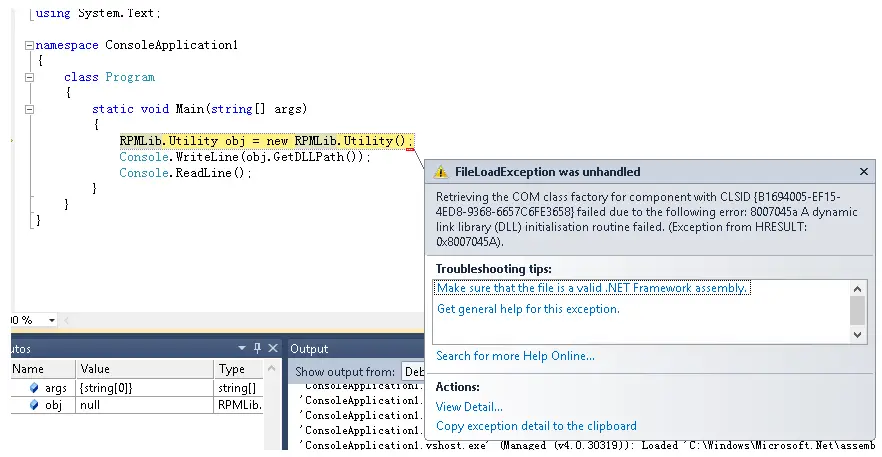
The COM initialization will fail after the detection. The following is the very basic C# Win32 .NET 4.0 Application that tries to call a COM object but fails without luck because VMP detects the Visual Studio as a ‘debugger’.
–EOF (The Ultimate Computing & Technology Blog) —
391 wordsLast Post: Delphi COM object private attributes not accessible in multithreading
Next Post: Lock Serial Number to Hardware in Licensing using VMProtect