Well, the SSL (Secure Socket Layer) is the future for internet (blogs, websites etc). The SSL connections are secure meaning that it is almost impossible to crack/interpret the content sent and received over the networks. The HTTP is not apparently and any decent hacker or network sniffers know the content of communication easily and it would be a problem imaging if you are sending username and password over HTTP not HTTPS.
To enable SSL, you would need to purchase certificates and the first thing is to generate the Certificate Signing Request (CSR). If you are using OpenSSL, You could try:
Type the following command to generate a private key.
1 | # openssl genrsa -out ~/helloacm.com.ssl/helloacm.com.key 2048 |
# openssl genrsa -out ~/helloacm.com.ssl/helloacm.com.key 2048
Create a CSR
Type the following command to create a CSR with the RSA private key (output will be PEM format):
1 | # openssl req -new -key ~/helloacm.com.ssl/domain.com.key -out ~/helloacm.com.ssl/helloacm.com.csr |
# openssl req -new -key ~/helloacm.com.ssl/domain.com.key -out ~/helloacm.com.ssl/helloacm.com.csr
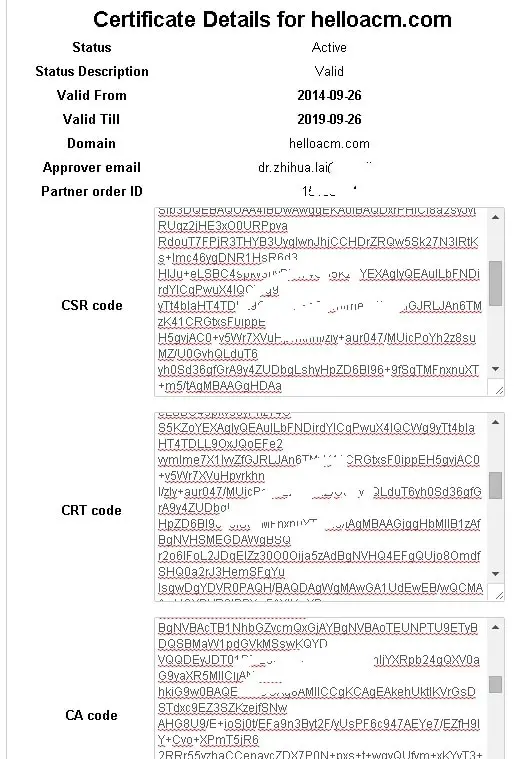
Now, follow the instructions in control panel of your web hosting provider, you should be able to receive a few certificates.
Now you need to enable the SSL module for apache2 server. Run the command using root.
1 | a2enmod ssl |
a2enmod ssl
Module ssl installed; run /etc/init.d/apache2 force-reload to enable.
Save the contents of CSR, CA, and CRT into a folder i.e.
/var/www/ssl and change the /etc/apache2/sites-availble/default-ssl.conf
You only need to include the .CRT and CA not the .CSR. Again depending on your setup you could also use (SSLCertificateChainFile):
1 2 3 4 | SSLEngine on SSLCertificateFile /var/www/ssl/crt/primary.crt SSLCertificateKeyFile /var/www/crt/private.key SSLCertificateChainFile /var/www/crt/intermediate.crt |
SSLEngine on SSLCertificateFile /var/www/ssl/crt/primary.crt SSLCertificateKeyFile /var/www/crt/private.key SSLCertificateChainFile /var/www/crt/intermediate.crt
SSLCertificateFile should be your primary certificate file for your domain name.
SSLCertificateKeyFile should be the key file generated when you created the CSR.
SSLCertificateChainFile should be the intermediate certificate file “CA Code” that was supplied by your certificate authority Comodo.
Be sure to restart your Apache web server after each modification.
1 | sudo service apache2 restart |
sudo service apache2 restart
Alternatively,
1 | /etc/init.d/apache2 restart |
/etc/init.d/apache2 restart
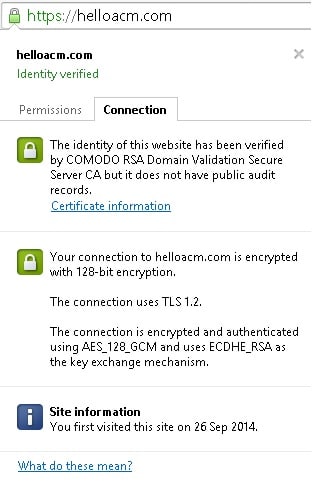
You should be able to use HTTPS after above steps.
–EOF (The Ultimate Computing & Technology Blog) —
loading...
Last Post: The Domains and Webhosting History
Next Post: How to Make a Page Fully Secure over SSL Connections?